Foram encontradas 60 questões.
- Interpretação de texto | Reading comprehension
- Gramática - Língua InglesaAdvérbios e conjunções | Adverbs and conjunctions
Cybersecurity: An overview of cyber challenges facing the nation, and actions needed
Federal agencies and the nation’s critical infrastructure — such as energy, transportation systems, communications, and financial services — depend on Information Technology (IT) systems to carry out operations and process essential data. However, the risks to these IT systems are increasing—including insider threats from witting or unwitting employees, escalating and emerging threats from around the globe, and the emergence of new and more destructive attacks. Rapid developments in new technologies, such as artificial intelligence, the Internet of Things, and ubiquitous Internet and cellular connectivity, can also introduce security issues. Over 28,000 security incidents were reported by federal civilian agencies to the Department of Homeland Security in FY 2019.
Additionally, since many government IT systems contain vast amounts of personally identifiable information (PII), federal agencies must protect the confidentiality, integrity, and availability of this information—and effectively respond to data breaches and security incidents. Likewise, the trend in the private sector of collecting extensive and detailed information about individuals needs appropriate limits.
To highlight the importance of these issues, Government Accountability Office (GAO) has designated information security as a government-wide high-risk area since 1997. This high-risk area was expanded in 2003 to include the protection of critical cyber infrastructure and, in 2015, to include protecting the privacy of PII.
GAO has made about 3,300 recommendations to federal agencies to address cybersecurity shortcomings—and we reported that more than 750 of these had not been fully implemented as of December 2020. We designated 67 as priority, meaning that we believe they warrant priority attention from heads of key departments and agencies.
Adapted from: https://www.gao.gov/cybersecurity. Available on November 16th, 2022
Provas
Cybersecurity: An overview of cyber challenges facing the nation, and actions needed
Federal agencies and the nation’s critical infrastructure — such as energy, transportation systems, communications, and financial services — depend on Information Technology (IT) systems to carry out operations and process essential data. However, the risks to these IT systems are increasing—including insider threats from witting or unwitting employees, escalating and emerging threats from around the globe, and the emergence of new and more destructive attacks. Rapid developments in new technologies, such as artificial intelligence, the Internet of Things, and ubiquitous Internet and cellular connectivity, can also introduce security issues. Over 28,000 security incidents were reported by federal civilian agencies to the Department of Homeland Security in FY 2019.
Additionally, since many government IT systems contain vast amounts of personally identifiable information (PII), federal agencies must protect the confidentiality, integrity, and availability of this information—and effectively respond to data breaches and security incidents. Likewise, the trend in the private sector of collecting extensive and detailed information about individuals needs appropriate limits.
To highlight the importance of these issues, Government Accountability Office (GAO) has designated information security as a government-wide high-risk area since 1997. This high-risk area was expanded in 2003 to include the protection of critical cyber infrastructure and, in 2015, to include protecting the privacy of PII.
GAO has made about 3,300 recommendations to federal agencies to address cybersecurity shortcomings—and we reported that more than 750 of these had not been fully implemented as of December 2020. We designated 67 as priority, meaning that we believe they warrant priority attention from heads of key departments and agencies.
Adapted from: https://www.gao.gov/cybersecurity. Available on November 16th, 2022
Provas
Cybersecurity: An overview of cyber challenges facing the nation, and actions needed
Federal agencies and the nation’s critical infrastructure — such as energy, transportation systems, communications, and financial services — depend on Information Technology (IT) systems to carry out operations and process essential data. However, the risks to these IT systems are increasing—including insider threats from witting or unwitting employees, escalating and emerging threats from around the globe, and the emergence of new and more destructive attacks. Rapid developments in new technologies, such as artificial intelligence, the Internet of Things, and ubiquitous Internet and cellular connectivity, can also introduce security issues. Over 28,000 security incidents were reported by federal civilian agencies to the Department of Homeland Security in FY 2019.
Additionally, since many government IT systems contain vast amounts of personally identifiable information (PII), federal agencies must protect the confidentiality, integrity, and availability of this information—and effectively respond to data breaches and security incidents. Likewise, the trend in the private sector of collecting extensive and detailed information about individuals needs appropriate limits.
To highlight the importance of these issues, Government Accountability Office (GAO) has designated information security as a government-wide high-risk area since 1997. This high-risk area was expanded in 2003 to include the protection of critical cyber infrastructure and, in 2015, to include protecting the privacy of PII.
GAO has made about 3,300 recommendations to federal agencies to address cybersecurity shortcomings—and we reported that more than 750 of these had not been fully implemented as of December 2020. We designated 67 as priority, meaning that we believe they warrant priority attention from heads of key departments and agencies.
Adapted from: https://www.gao.gov/cybersecurity. Available on November 16th, 2022
Provas
Cybersecurity: An overview of cyber challenges facing the nation, and actions needed
Federal agencies and the nation’s critical infrastructure — such as energy, transportation systems, communications, and financial services — depend on Information Technology (IT) systems to carry out operations and process essential data. However, the risks to these IT systems are increasing—including insider threats from witting or unwitting employees, escalating and emerging threats from around the globe, and the emergence of new and more destructive attacks. Rapid developments in new technologies, such as artificial intelligence, the Internet of Things, and ubiquitous Internet and cellular connectivity, can also introduce security issues. Over 28,000 security incidents were reported by federal civilian agencies to the Department of Homeland Security in FY 2019.
Additionally, since many government IT systems contain vast amounts of personally identifiable information (PII), federal agencies must protect the confidentiality, integrity, and availability of this information—and effectively respond to data breaches and security incidents. Likewise, the trend in the private sector of collecting extensive and detailed information about individuals needs appropriate limits.
To highlight the importance of these issues, Government Accountability Office (GAO) has designated information security as a government-wide high-risk area since 1997. This high-risk area was expanded in 2003 to include the protection of critical cyber infrastructure and, in 2015, to include protecting the privacy of PII.
GAO has made about 3,300 recommendations to federal agencies to address cybersecurity shortcomings—and we reported that more than 750 of these had not been fully implemented as of December 2020. We designated 67 as priority, meaning that we believe they warrant priority attention from heads of key departments and agencies.
Adapted from: https://www.gao.gov/cybersecurity. Available on November 16th, 2022
According to the text, the escalating threats to IT systems
Provas
Provas
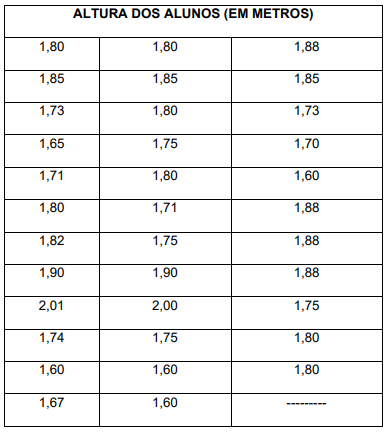
A altura mediana é igual a:
Provas
Para estruturar determinada armação de madeira em vigas de sustentação do telhado de um salão de jogos do clube, o planejamento foi desenhado previamente no seguinte projeto:
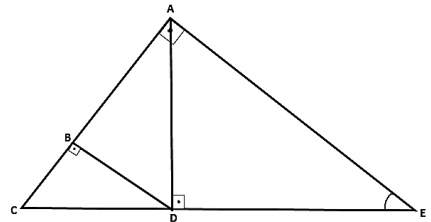
Considerando que o desenho acima está na escala 1:20 e que a medida CE, no desenho, é igual a 80 cm e que o ângulo AÊD é igual a 30º , o comprimento BC de madeira que deverá ser cortada para compor a estrutura deverá ser igual a
Provas
Leia o trecho a seguir:
“O livro inédito mais grosso do mundo: O Das Buch des dickste Universums, editado pela Zeitgeist Media GMBH, reúne textos e desenhos feitos por crianças num concurso realizado pelo Ministério Federal dos Transportes da Alemanha. A singela lombada do livro mede míseros 4,08 metros. Tem 50.560 páginas e pesa 220 kg. Você pode encomendá-lo em qualquer livraria da Alemanha pela bagatela de 9.999 Euros.”
Fonte>https://www.designdoescritor.com/post/2019/10/23/10-recordes-liter%C3%A1riosregistrados-pelo-guinness-book
Pedro decidiu bolar um trabalho pedagógico, moldando um desafio sobre o assunto, propondo para seus alunos a seguinte questão: “Considere um livro enigmático em que os números de páginas não iniciem da página 1, mas que sejam todos de cinco algarismos distintos, formados e dispostos utilizando-se apenas os algarismos ímpares 1, 3, 5, 7 e 9. Organizando essas páginas em ordem crescente, dentre todos os números de página que se pode obter permutando esses algarismos, o número 75.391 ocuparia, nessa disposição, qual lugar?”
Provas
Provas
Provas
Caderno Container